I've had a new request in recently, as part of a move to SCEP + Certificates (away from pre-shared keys) a customer has asked if we could use the PKI CA build into Cisco's router IOS. Now is this is a new idea to me; in the past people have either "plumped" for Microsofts CA implementation or cooked something up themselves with openssl.
Cisco's IOS Security Guide (you may need a CCO Login) clearly states that it's possible and that it supports SCEP auto-enrolment, so I thought I'd give it a go!
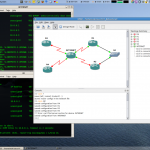
I don't have any routers available at the moment, but I've been able to get things tested within gns3 ( gns3 screen shot). What I've done is setup a basic implementation, I have a router called "CA" which would be the root certificate authority, which would typically be on the inside of your network; then I have a router called "VPN_A", this router would be the HQ VPN Termination device, it would be where all the remote (or branch) routers connect to, this router is configured with SCEP and is able to HTTP download the CRL from CA. The final router is "VPN_B" this router has been enrolled manually with a "copy / paste" and does not have HTTP Access to the CA, below is a screen shot of what I've done.
Example configs and a .net config file, which can be imported into gns3 (with a little tweaking) are available in my cisco directory, hopefully these examples give enough detail on how to manually or automatically enroll the routers and setup and IPSEC VPN, obviously they're not complete configs (no usernames & pass's set for a start) but there should be enough for someone to integrate this into their existing templates.